The Kill Chain
From Terrorist to Targeted Drone Attack
The Kill Chain
Written by Peter Bowen
In EYE IN THE SKY, Helen Mirren plays UK Colonel Katherine Powell who is tracking a British national, Susan Danford (Lex King), suspected of working with the East African terrorist group Al-Shabaab. The operation is a complex and coordinated effort between different countries. On the ground, Kenyan intelligence operatives, like Jama Farah (Barkhad Abdi), keep an eye on the suspects. From the air, US Air Force pilots, like Lt. Steve Watts (Aaron Paul), remotely fly drones from a Nevada bunker to provide an eye in the sky. In London, Powell coordinates these various forces, as well as communicates to a panel of government officials above her. Her supervisor, Lieutenant General Frank Benson (Alan Rickman), observes the operation remotely with a select group tasked with providing judicial and government oversight. UK Attorney General George Matherson (Richard McCabe) adjudicates the legality of the unfolding operation, while Minister of State for Foreign and Commonwealth Affairs Brian Woodale (Jeremy Northam) and Parliamentary Under Secretary of State Angela Northam (Monica Dolan) oversee the optics and ethics of the mission.

When the mission moves from an operation of capture to becoming a targeted kill, the lines of authority start to get a bit blurred. Questions of collateral damage and media fallout push the operation up the kill chain to British Foreign Minister James Willet (Iain Glen) and across the pond to US officials like Senior Legal Advisor on the US National Security Council Jillian Goldman (Laila Robins) and US Secretary of State Ken Stanitzke (Michael O'Keefe). Screenwriter Guy Hibbert and director Gavin Hood worked to mirror their film as accurately as possible to the actual line of command that such an operation would entail. To assist them, they enlisted the help of two military advisors with over 25 years of experience – one American, one British – to confirm and check every detail. “We wanted to make sure we were correct as much as possible in every aspect of how the ‘Kill Chain’ works politically,” says producer Ged Doherty.
Since 2001, when the first drone was used as a combat weapon, governments have wrestled with how to authorize their use within conventional rules of engagement. Shortly after 9/11 in the United States, a joint congressional resolution termed the “Authorization for Use of Military Force Against Terrorists (AUMF)” provided the general legal framework for the future use of drones. In the AUMF, “the President is authorized to use all necessary and appropriate force against those nations, organizations, or persons he determines planned, authorized, committed, or aided the terrorist attacks that occurred on September 11, 2001, or harbored such organizations or persons, in order to prevent any future acts of international terrorism against the United States by such nations, organizations or persons.” While the resolution’s language singles out the terrorists responsible for 9/11, the AUMF continues to provide a license for the overall war on terror, whether the targets be al-Qaeda, ISIS or Al-Shabaab.
When military and intelligence agencies shifted their focus away from the hot battlefields in Afghanistan and Iraq to specific targets in Africa and the Middle East, AUMF continued to provide a legal framework for drone attacks. In 2012, John O. Brennan, Assistant to the President for Homeland Security and Counterterrorism, explicitly cited the AUMF as a defense of drones in a speech entitled "The Ethics and Efficacy of the President’s Counterterrorism Strategy." Brennan stated, “The United States is in an armed conflict with al-Qaeda, the Taliban, and associated forces... There is nothing in international law that bans the use of remotely piloted aircraft for this purpose or that prohibits us from using lethal force against our enemies outside of an active battlefield, at least when the country involved consents or is unable or unwilling to take action against the threat." Drone technology would no longer simply be another weapon in the army’s arsenal, but now a strategic tool deployed to surgically eliminate specific individuals on the government’s kill list. In 2012, The New York Times, in an article about a new “Secret ‘Kill List,’” pointed out: “Mr. Obama has placed himself at the helm of a top secret “nominations” process to designate terrorists for kill or capture, of which the capture part has become largely theoretical.”Acknowledging that such attacks unfortunately also kill civilians, President Obama expressed in a speech at the National Defense University, “These deaths will haunt us. But as commander-in-chief, I must weigh these heartbreaking tragedies against the alternative. To do nothing in the face of terrorist networks would invite far more civilian casualties." In time, a kill chain emerged both for identifying potential terrorist targets and for authorizing drone attacks against them.
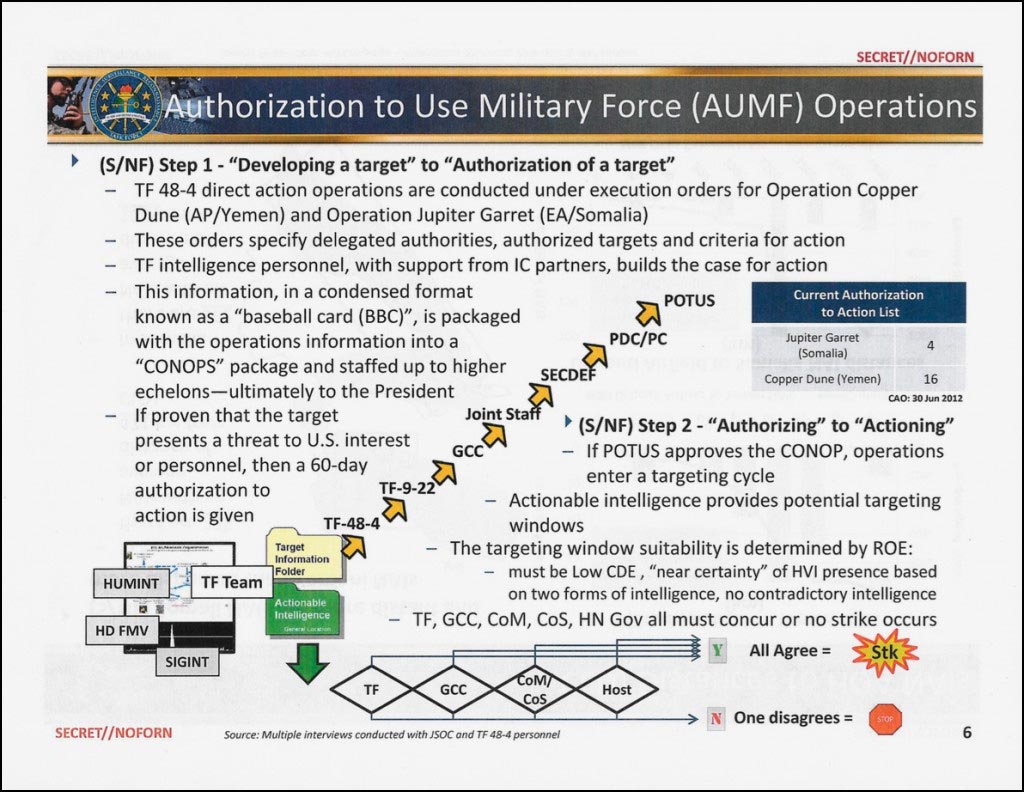
In 2015, the website The Intercept published “The Drone Papers,” which included a slide from a 2013 Pentagon presentation entitled “Authorization to Use Military Force (AUMF) Operations.” The diagram illustrates the two-step process by which a target is first developed and then an operation authorized by the President of the United States before a strike is launched against that target. While detailing specifically the Joint Special Operations Command (JSOC) campaign in Yemen and Somalia, this kill chain diagram provides a privileged glimpse into the gritty details of drone attacks. To understand the trajectory of step one, we follow the kill chain’s path from bottom to top, seeing how intelligence gathered at a local level eventually lands on the President’s desk. TF-48, the first rung on the chain, is the task force dealing with East Africa. This leads up to GCC (or Geographic Combatant Commanders), the group that oversees the Unified Command Plan that defines military authority by geographical area. SECDEF (or Secretary of Defense) then moves this intelligence from the military arena into the executive office with “PDC/PC” (or the Principals Committee), a group composed of the five main members of the National Security Council. Finally, the intelligence is presented to the President of the United States, who must authorize action. In Step 2, an operation is planned and executed. Here the diagram highlights the number of checks and balances each operation must undergo as part of the ROE (or Rules of Engagement). Not only must the mission determine there is a “Low CDE” (or Collateral Damage Estimate), but must also guarantee a “near certainty” of hitting the HVI (high value individual). In addition, all parties at all levels – including TF (Task Force), GCC (Geographic Combatant Commanders), CoM (Chief of Mission), CoS (Chief of Staff) and HN Gov (Home Nation Government) – must agree with the mission. If one disagrees, the mission is scrapped.
While this kill chain illustrates how a targeted kill is handled in the US, Britain (as EYE IN THE SKY illustrates) follows a slightly different protocol. In the 2015 article “Britain conducts a drone assassination,” The Economist headlines how the UK will be extending drones attacks “but will not be imitating America.” In the article, Prime Minister David Cameron defends the targeted kill of Reyaad Khan, an ISIS fighter and British citizen, by highlighting the means by which the attack were justified. In addition to confirming intelligence about the imminent threat posed by Khan, the government sought a ruling from Attorney General Jeremy Wright confirming, “there would be a clear legal basis for action under international law”. Moreover, The Economisthighlights that Prime Minister Cameron would not be “seeking the wide powers granted to American presidents after 9/11 to kill the country’s enemies wherever they may be found.” Indeed this strike, as The Economistnotes, “was not carried out by an intelligence agency, but by the RAF operating through a clear chain of command.”


